DNS is vulnerable – Cannot be trusted, no improvements since 1983 and usage of functionality and quantity has widened.
Risks | No DNS – no webpage
| Wrong DNS – wrong webpage
Besides, security fails with Opportunistic Encryption which leads to unauthorized and compromised certificates, Man-in-the-Middle attacker may downgrade session to non-TLS at the time of email communications.

Hacker can intercept TLS communication by mapping certificate from the way of MITM and improper configurations accepts self-signed certificates.
DANE is a technology that might change our present and future. It’s a DNSSEC trust scheme for X.509 certificates that provide encrypted email communications.
DANE – DNS based Authentication of Named Entities provides layered security by fastening the X.509 certificate of a website to the DNS. This channel provides details about X.509 certificate to the user who can use to validate certificate.
DANE uses DNSSEC —-> DNS turn into policy channel —-> DNSSEC affix trust layer
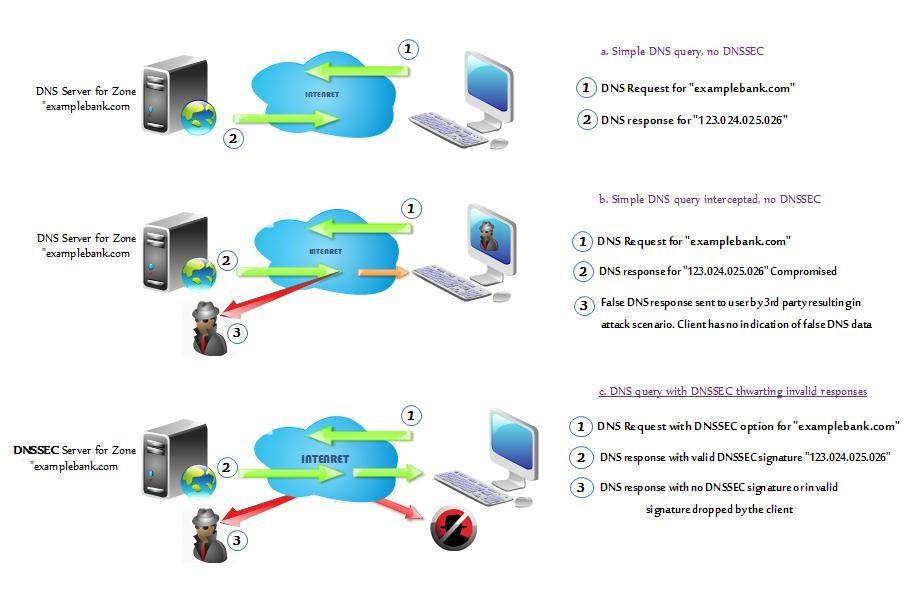
DNSSEC – DNS Security Extensions (DNSSEC) adds security to the DNS by embodying public key cryptography into the DNS hierarchy. When carried out via an attack on a network’s or an ISP’s infrastructure, all of the entity’s users are affected. This is often referred to as DNS cache poisoning, DNS malware borne attacks, Man in the Middle attacks and DNS redirection/DNS spoofing.
NCDRC’S TAKE ON DNSSEC AND DANE
At, National Cyber Defense Research Center, we have tested DNSSEC validation on our resolvers by using Bind9, Mozilla, Chrome and Gateway, which means our resolvers always validate queries for domains that have been signed using DNSSEC. Users automatically benefit as soon as a domain is signed using DNSSEC.
So far techies deploying DNSSEC on their domain names – “sign” domain names or ask Registrar for DNSSEC (Enable DNSSEC validation on originations/ISP DNS resolvers). World really needs lots of DNS resolvers. Besides, ask ISP about DNSSEC and support on their ISP DNS resolvers.
Both DNSSEC and SSL depend on public key cryptography. DNSSEC deals with “where”, and SSL deals with “how” and “who”.
Testing results: Below image explains the process of with DNSSEC and without.
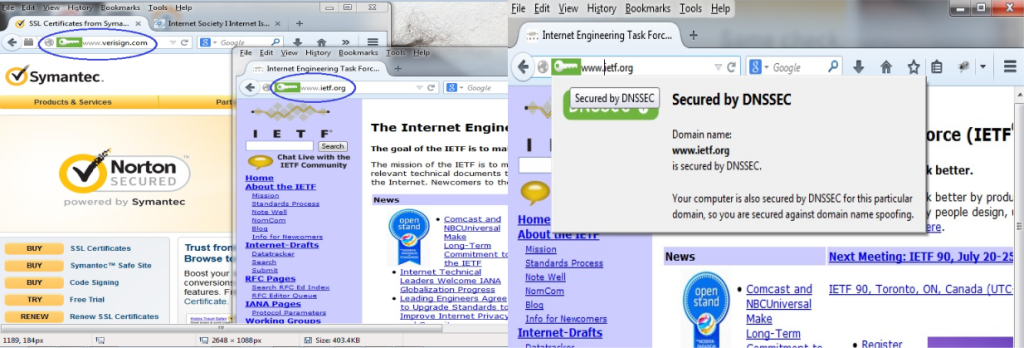
Below image is the proof of concept tested on Mozilla Firefox browser with DNSSEC validator
DANE is targeted by Security providers, Government or Private Email users with known security needs, Online-Payment sites, insurance providers, banks, Enterprises and Internet of Things
DANE is the de-facto standard technology.
About the Author –

Aravindh Subramanian
Aravindh is experienced in Offensive Security and Cloud-centric cybersecurity strategies to achieve cost benefits that reduce risk and exposure to threats. He empowers healthcare organizations avoid potential financial loss from their data being misused in the cloud and from being non-compliant.
In his lesuire time, he loves road trips and listening to music.
Back to blogs
