“The next world war presumably would be a Cyber War “
Cybercrime is increasing at an appalling rate. The burgeoning internet, cloud services, networks and connected devices would explode in next few years generating volumes of data (Big Data) and this information must be protected. The future cyber security must be smarter since new vulnerabilities mean new opportunities.
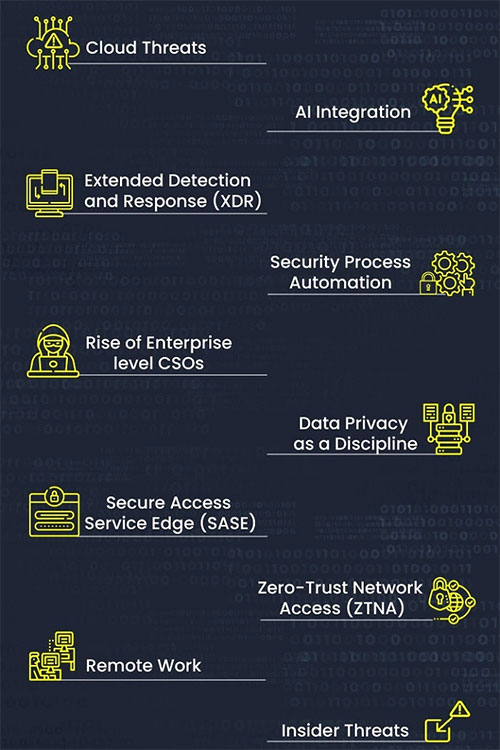
Trends 2021
- Per IDC, the global cloud services market spending is projected to reach USD 1 trillion in 2024, at a CAGR of 15.7% during 2020-24.
- Per market estimates, AI in the cybersecurity market is projected to grow from USD 8.8 billion in 2019 to USD 38.2 billion by 2026 at a CAGR of 23.3%.
- The Extended Detection and Response (XDR) is set to gain momentum as they can automatically collect data from multiple endpoints and correlate them to facilitate faster threat detection and incident response.
- Per the Cybersecurity Ventures, the cybersecurity talent crunch is expected to create 3.5 million unfilled cybersecurity jobs by 2021, up by 350% from 1 million positions in 2014.
- The CSO can bring physical security, IT security, OT security, product management security, and supply chain security into a centralized governance model.
- As a standalone discipline, data privacy impact almost all aspects of an organization, from co-directing the corporate strategy to closely aligning with security, HR, governance, and procurement.
- Per Gartner, around 40% of businesses will adopt explicit strategies for implementing SASE by 2024, from <1% in 2018.
- Per Gartner, 80% of new digital business applications will be accessed through ZTNA by 2020, and 60% of enterprises will move from remote-access VPNs to ZTNA by 2023.
- Per Gartner, 88% of global business organizations mandated or encouraged all their employees to work from home due to the pandemic.
- Per Forrester, insider data breaches are poised to increase by 8% in 2021 and account for 33% of all cybersecurity incidents.
Future of Cybersecurity solutions
There have been multitudinous ground-breaking cybersecurity solutions. NIST (National Institute of Standards and Technology) implements practical cybersecurity and privacy through outreach and effective application of standards and best practices necessary to adopt cybersecurity capabilities. Zero Trust Architecture network model is one such NIST approved security model.
Zero Trust Architecture | Security for a new world
Network security protocols help to protect information from malicious actors outside its network but provides almost unrestricted access to users and devices inside. These traditional architectures build multiple layers of security like firewalls, Network Access Control (NAC) and Virtual Private Networks (VPNs) to protect unauthorized access of outsiders but none from insiders. Some of the attack progressions of the traditional architecture are:
- Phishing emails attack on employees
- Compromised privileged machine
- Keylogger installed on corporate machines
- Developer password is compromised
- Production environment is compromised using privileged machine
- Database credentials compromised
- Exfiltration via compromised cloud hosting service and so on
The solution to prevent these insider threats is “ZERO TRUST”.
As the image indicates in zero trust architecture, none is believed without genuine verification and validation.
- From the query performance perspective this model is one of the most efficient, because the DBAs have complete control of the data and with the techniques like partitioning, indexing they could ensure that the query can be done in the best possible manner. Since the hardware is fully owned by a single organization (which is the HIE itself), this can be scaled out or scaled up to meet the demands of the business.
- This model is fairly self-sufficient once the mechanism for the data transfers are established, as the need to connect to individual hospitals are no longer there.
- Smaller hospitals in the ecosystem need not take the burden of maintaining their data and interoperability needs and can just send their data to the centralized repository.
- Better scope for performing population predictive and prescriptive analytics as the data resides in one place and easier to create models based on the historical data.
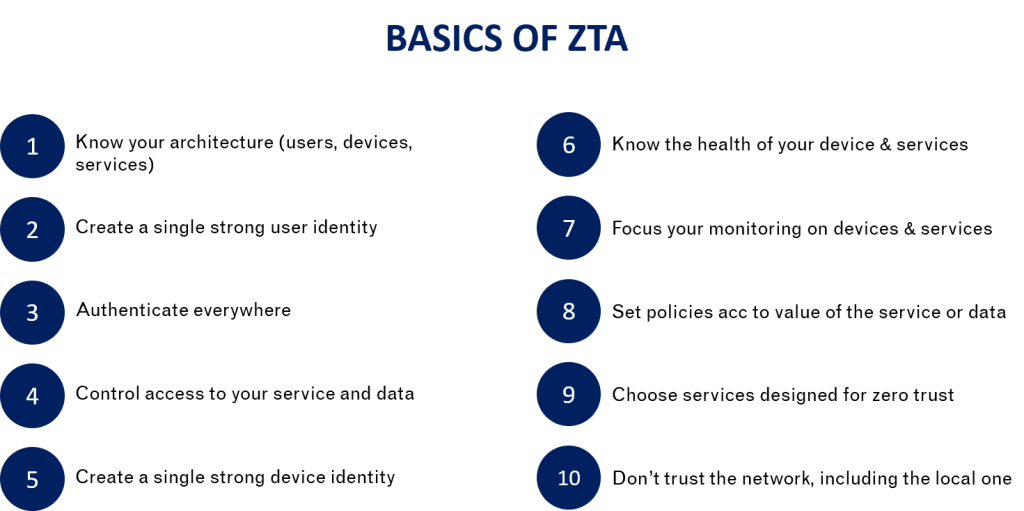
Fundamentals of Zero Trust Architecture (ZTA)
“Zero trust” was coined by John Kindervag in 2010. He proposed that companies should move away from perimeter-centric network security approaches to a model that involves continuous trust verification mechanisms across every user, device, layer, and application.
De-centralized HIE Data Model
Zero Trust Architecture

Key Factors of Zero Trust model
Access to infra or application is enabled only for
- authorized users irrespective of their job roles (end users, privileged user, outsourced IT, partner, Customer etc) via secure authentication like Passwordless,
- authorized assets,
- required resources and required period.
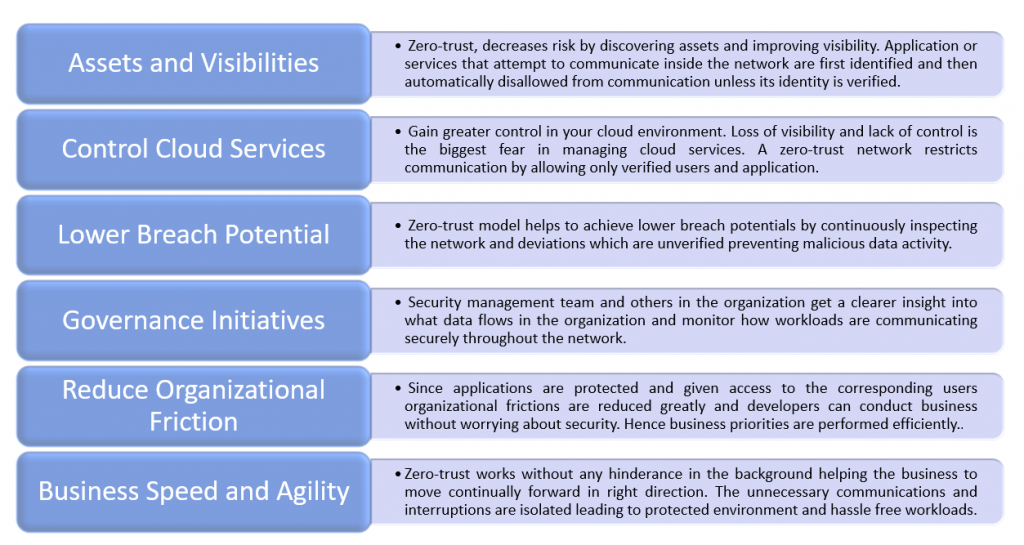
Benefits of Zero Trust Architecture
Building a ZTA
Deploying ZTA is incorrectly perceived as a costly process that hinders the daily activities of the organization. But zero trust is built upon the existing network without removing or replacing any components.
- Define Protect Surface
The protect surface must be defined to manage the expanding threat landscapes. The most valuable information encompassing critical Data, Applications, Assets and Services (DaaS). - Define the flow of architecture
The direction of the data flow, network traffic must be analyzed and defined. Defining this architecture makes it easy to implement Zero Trust since it provides a clear insight of the network. - Architect the zero-trust architecture
ZTA does not have any universal pattern. It is customized per the business needs. With the help of protection surface definitions and flow definitions the Zero trust becomes logical to implement. - Create Zero Trust Policies
Zero Trust policies are created using the ‘Kipling Method’ to whitelist resources that should have access to others. Kipling suggested the concept of “who, what, when, where, why and how” in his poem “Six Serving Men.” Using this concept, the following questions are defined in the architecture.
- Who should access a resource?
- What application is used to access a resource inside the protected surface?
- When is the resource accessed?
- Where is the data destination?
- Why is this application trying to access this resource within the protect surface?
- How is the packet accessing the protect surface via a specific application?
- Monitoring and Maintaining the Architecture
This step includes reviewing all logs, focusing on the operational aspects of Zero Trust. Since Zero Trust is an iterative process, inspecting and logging all traffic will provide valuable insights into how to improve the network overtime.
Once the architecture is implemented for the first protect surface, it can be expanded iteratively move other data, applications, assets, or services from your legacy network to a Zero Trust network in a way that is cost-effective and non-disruptive.
Implementation of ZTA
- Micro-segmentation:
The network or the data centre is divided into smaller independent units that can be secured with different access credentials and policies in addition to VPNs, NAC, and Firewalls etc. - Verify Users and Devices:
The users and the devices performing on the network are to be verified using strict authentication and authorization. When the device or user fails to be verified, its eliminated or isolated. - Multi-factor authentication:
MFA is more secure than just a password including Biometrics and OTP are MFA methods. - Principle of Least Privilege (PoLP):
The principle of least privilege (PoLP) is the process of limiting access rights for users with minimum permissions they need to perform work. Under PoLP, we can control the read, write, or execute only the files/resources they need for work.
Conclusion Observations
ZTA is an evolutionary framework built on existing security concepts and does not introduce a radical new approach to cybersecurity. ZTA relies on a fundamental understanding of an organization’s services, data, users, and endpoints to be effective. In ZTA, elements such as Software Defined Networking and Identity, Credential, and Access Management are essential components for a successful long term ZTA strategy. It can complement other cybersecurity tools and practices rather than replacing them. Threat intelligence, continuous monitoring, and Red Teaming exercises remain important components to Zero Trust Networking environments and a comprehensive security approach.
ZTA is a powerful mature strategy that can provide a positive cybersecurity return on investment, but it may require up-front investments depending on what is already in place.
Sources
⦁ https://www.microsoft.com/en-gb/security/business/zero-trust
⦁ https://www.tag-cyber.com/media/charlie-ciso/zero-trust-security
About the Author –

Vishnu Raj
Vishnu Raj is a part of the GAVS Security Practice (Red Team Member). He’s passionate about building secure apps as he believes everyone deserves privacy.
Back to blogs
