
Ageing and obsolete devices create security vulnerabilities and put businesses at risk of cyber-attacks. The growing use of open and co-working spaces and the existence of obsolete devices exacerbate the risks.
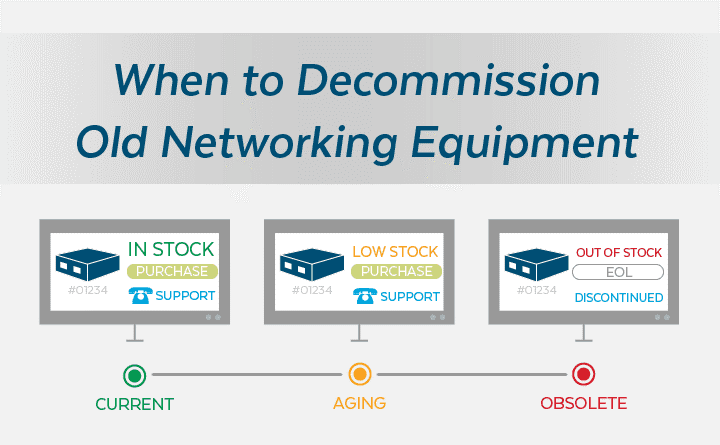
Listed below are the kinds of devices in any organization.
- Current: Devices are currently on the market and can be actively maintained. The vendors provide some software patches and updates, and there is a maintenance contract that can be attached to it.
- Ageing: Devices that vendors no longer sell, but still actively support. We can attach some form of maintenance contract to it. If there’s vulnerability, they’ll release a software patch for it. It there are new features or specific bugs that need to be addressed, they’ll actively push out software updates for those.
- Obsolete: Devices that are no longer sold and supported by the vendor. So, there is no software updates released for it, no security, vulnerabilities fixed, etc.
On an average, an obsolete device has twice as many vulnerabilities per device (42.2%) compared to ageing (26.8%) and current devices (19.4%).
2020 Global Network Insights Report
- Nearly 46.3% of organizations’ networking assets are ageing or obsolete globally, compared with 4.3% in 2017, signalling prolonged refresh cycles as business sweat assets and move to multi-cloud environments.
- Organizations in the technology sector which are usually the first to adopt new products are the most affected. The sector’s percentage of ageing and obsolete devices was also high at 59.6% in 2019.
- The other sector that is ahead is the public sector with 61.7% ageing and obsolete devices. Healthcare (52.5%), energy & utilities (51.9%) and retail & wholesale (49.1%) are the other three sectors with a high percentage of such devices, above the industry average of 47.9%.
The Achilles Heel of Healthcare Cybersecurity
Cyber threat actors and criminals are always on the lookout to exploit the vulnerabilities that plague the healthcare sector.
While shared healthcare information aid in providing top-quality medical care, it also puts the patients at risk of getting their data stolen and misused.

Why is Healthcare Information a Target for Cyber Attacks?
- Valuable financial information can be obtained from medical provider networks.
- Owing to the nature of the healthcare industry, nearly everyone’s personal information can be obtained in some form.
- The interconnected nature of EHRs means hackers have access to the data that has collected under patient’s names for years. Sharing patient information is integral to providing the best possible treatment to patients, but that same sharing also makes networks extremely valuable targets.

Growing Concerns over Proliferation of Connected Devices
Most hospitals have hundreds or thousands of medical devices in use enabling a variety of functions. Furthermore, healthcare IT environments have shifted from a homogenous makeup to a more heterogeneous makeup with a variety of operating systems, different types of devices, cloud-based applications and services, and behavioral-based security tools/technologies. This causes medical IT networks to be complicated and potentially the most vulnerable access point in a medical facility’s infrastructure.
A report by MarketsAndMarkets anticipates a combined annual growth rate of 27.6% for healthcare IoT devices from 2019 to 2024. As medical technologies advance at an impressive rate, cybersecurity efforts have to keep pace so that medical facilities operate smoothly and patients stay safe.
Connected devices like infusion pumps, heart rate monitors, and even imaging and biopsy tables have become a critical part of the healthcare environment. But these put patient data and potentially patient well-being at risk.

Threat to Healthcare Organizations
- As the Internet of Medical Things (IoMT) grows, data from medical devices like infusion pumps export information to external sources and interact with the world outside the doctor’s office. This data could be intercepted or manipulated, creating a host of issues. Moreover, hackers could gain access to manage most items connected to the network, including how the machines function.
- Tight budgets are a reason why outdated devices service longer than they should. Obviously, using legacy devices is not the safest option when it comes to patient care and information. Newer risks are emerging as many legacy devices and systems are increasing the attack surfaces for cybercriminals.
- Old devices that have unsupported systems and are no longer receiving updates are becoming an entryway for hackers. Generally, devices that have software applications which do not receive security patches is a massive potential threat.
- Often small to medium-sized organizations with limited budgets fail to patch devices. Some organizations choose not to patch even with known security risks, as some critical software in health care may not work properly on the newer version of operating system.
Mitigations
- No one is monitoring their healthcare devices from the presence of an attacker. No one is thinking about CT scanner or MRI machine as launchpad for broader attack. So, there is a need to establish a process for monitoring the lifecycle stages of equipment and to develop a database and assign experts within the organization to collect and maintain the information.
- Medical devices like monitoring machines that have been on the market for years need to be secured by security scanning, and an easy mechanism for regular downloading and updating security patches.
- There is a need in providing incentives for future generations of devices to include more robust security protections from the start. Manufacturers ignore the security in the early planning stages or rely on third-party components that may be vulnerable themselves.
- It has been suggested that machine learning and AI can play a massive role in mitigating the risks posed by both the deployment of new IoT devices as well as legacy technologies and systems. In particular, the best way to assess potential threats is through privileged access controls.
- By managing privilege —the accounts, credentials, and secrets that can give users wide-ranging powers on a network or device — healthcare IT security can control access and privileges malicious actors need to access devices.

Despite these difficulties, interconnected networks of patient information will continue to grow. The results of information theft are too great to risk, making network and device security a principal goal of any healthcare organization.
References
- https://www.businesstoday.in/sectors/it/ageing-devices-biggest-threat-to-cybersecurity-as-work-from-home-becomes-norm/story/406552.html#:~:text=Even%20as%20adoption%20of%20new,spaces%20and%20remote%20work%20locations.
- https://www.zdnet.com/article/email-is-biggest-security-risk-old-devices-arent-getting-patched-and-local-cyber-incidents/
- https://telecom.economictimes.indiatimes.com/news/prolonged-device-upgrades-threaten-cyber-security-study/76279431
- https://futureiot.tech/surge-in-obsolete-network-devices-pose-cybersecurity-risk/
Sources
- https://tinyurl.com/y56znqnb
- https://tinyurl.com/y5n4jgqj
- https://tinyurl.com/y6nkudos
- https://tinyurl.com/y3upyf7v
- https://tinyurl.com/yxtbz8ht
- https://tinyurl.com/y57c7nyp
About the Author –

Vishnu Raj
Vishnu Raj is a part of the GAVS Security Practice (Red Team Member). He’s passionate about building secure apps as he believes everyone deserves privacy.
Back to blogs
