The increasingly digital world of ours is generating more data than ever. The data is generally stored in the cloud which can be accessed by certain devices. This makes the data vulnerable to hacking or cyber-attacks. Any malicious attempt to breach the information system of an individual or an organization would be termed a cyber-attack. Some of the common types of attacks include Malware, Phishing, Man-in-the-middle, Rogue Software, etc. Thus, Cybersecurity is important as it helps the users to secure data against malware and attacks by hackers.

AI-driven Cyber-attacks
Experts believe that there are enough technological resources and business motives to carry out a successful AI-driven cyber-attack. Black hats are turning to AI, using it to weaponize malware and attack the advancements in cybersecurity solutions. For example, AI is being used to conceal malicious code in applications. The concealed code is then executed after a time or when the application reaches a stage so that the magnitude of the impact from the attack is maximized. Masking such codes and information requires applying AI models.
Experts believe that hackers can also use an application feature such as voice or visual recognition, biometrics, and other identity management feature as an AI trigger for carrying out a cyber-attack. Since most applications have this feature, hackers use this to feed modified AI models, derive a key, and attack. These malicious AI models will be present for years without detection as hackers wait to strike when applications are vulnerable.
In addition to this, AI gathers information and adapt accordingly. Hackers leverage these capabilities to develop adaptable and intelligent malware. AI is used to collect information on its previous failures, thus enabling the malware to tweak itself as it propagates.
Hackers have developed new malware that stays undetected in a target machine using AI and records the information on the target machine especially mails from the same organization as the target is in. It uses this information to create a sophisticated email phishing attack that cannot be detected by SIEM tools. This type of malware continuously collects information and learns from it, making it hazardous.
Hackers use AI to create malware to mimic trusted system components that improve stealth attacks (by learning the computation environment, patch update lifecycle, communication protocols, and when the systems are vulnerable).
Prevention of Cyber-attacks
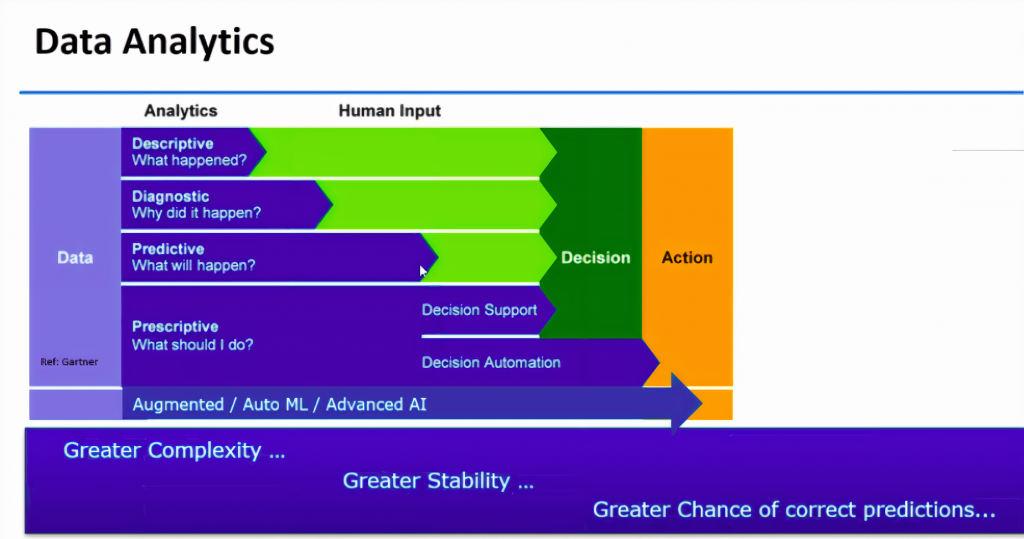
ML and AI applied to threat detection is the first step in identifying and preventing AI-driven cyber-attacks. TTP, threat actor payloads, and attacks are ever-changing. A solid intelligence approach to process big data, Indicators of compromise (IOCs) and their context, coupled with enrichment, reputational data, detonation data, and additional context is a huge undertaking. ML and AI can be used for the efficient processing of these data.
One possible use case involves the development of an ML/AI solution to detect a spam wave campaign. Common TTP for this involves abusing the email vector, multi-wave minor, and/or unique cryptographic checksum hash value malware variants and some common infrastructure if remote command and control infrastructure is used. ML and AI can be used to process huge data across multiple client environments and tickets in real-time, correspond the data, provide granular attribution, coupled with orchestration and automation actions like auto-escalate, auto-notify, and auto-defend actions. For example, if an endpoint is infected the AI system must automatically take it offline.
In February 2019, Microsoft successfully implemented ML (built into Windows Defense AV) to detect and mitigate the Emotet malware. Emotet is a mature threat that is well known for its polymorphic capabilities, making it impossible to detect the next variant in the campaign using the signature-based strategies. Detection of Emotet using AI was achieved through modeling in a decision tree, related to probabilities, weighted components, and calculations performed by a tool. It also included a real-time cloud ML across the Windows Defender complex ML models. This enabled deep learning and real-time protection within an AI solution set to successfully detect and block Emotet. There is great promise for AI when applied to advanced context and modeling as shown in this early real-world example.
AI as a solution
Security experts have conducted research to harness the capabilities of AI and incorporate it into security solutions. AI-enabled security tools and products have proved to detect and respond to cybersecurity incidents with minimal to zero input from humans and thus proving to be beneficial. Twenty-five percent of IT decision-makers attribute security as the primary reason why they adopt AI and ML in organizational cybersecurity. AI not only improves security posture, but it also automates detection and response processes. This reduces the finances and time spent in human-driven intervention and detection processes.
“AI technology makes entry-level jobs more interesting. AI can also help improve retention rates by making entry-level cybersecurity jobs “less dull,” says Kayne McGladrey, CISO and CIO of Pensar.
AI and ML can be used to review data and extract threads. Thus, entry-level professionals can focus on analyzing threats.
AI can be useful in research and analysis of large datasets because AI can sift through and address issues much faster and more efficiently than a person can.
Meanwhile, relieving individuals of such tasks allows them to do the work that humans are better suited for. Experts believe that AI is just another tool in a cybersecurity professional’s belt that enables them to concentrate on more critical and strategic work to be done in cybersecurity by relieving them of the more repetitive tasks.
AI must be adopted and implemented in a calculated fashion with an initial emphasis on manual execution and consistent outcomes. After this, organizations can implement orchestration components and automation towards long-term goals with AI. Implementation with poor-quality is a greater threat than AI-empowered malware today. As AI and ML increase their presence in the cybersecurity landscape, the organization’s defense will prevent them from becoming victims. This is especially true for organizations that embrace the need to transform, leveraging AI to help wade through big data, contextualized modeling, and decisions that need to be made to operationalize security.
Sources:
- https://www.cisomag.com/hackers-using-ai/
- https://symantec-enterprise-blogs.security.com/blogs/threat-intelligence/evolution-emotet-trojan-distributor
- https://www.xenonstack.com/blog/artificial-intelligence-cyber-security/
- https://www.cpomagazine.com/cyber-security/the-impact-of-artificial-intelligence-on-cyber-security/
- https://www.youtube.com/watch?v=ooPOOs7Y7lk
About the Authors:
Nagalakshmi VJ – Nagalakshmi is a python developer. Her keen interests include application penetration testing and learning new hacks. She is currently involved in product development
Ashwin Balaji Dhandapani – Ashwin Balaji is part of the red team wing of the security practice. His interests include Machine Learning and Artificial intelligence and are looking to efficiently harness ML and AI in cybersecurity practices.

Anjana K – Anjana is part of the red team wing of the security practice and is deeply interested in mobile application hacking and web application penetration testing.
Back to blogs
