Almost all software systems today face various threats, and the number of threats grows as technology changes. One disturbing trend is that 80% of the observed attacks in 2020 used software vulnerabilities, and the cost of damage due to cyber-crime is estimated to reach $6 trillion by the end of 2021. The administrator can use Threat-modeling methods to inform defensive measures.
Threat Modeling
- is a collection of security aspects
- is a set of alleged attacks that affects the performance of any computer system.
- allows security experts to identify potential risks and develop countermeasures in the design, coding, and testing phases
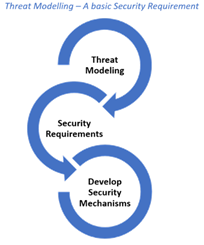
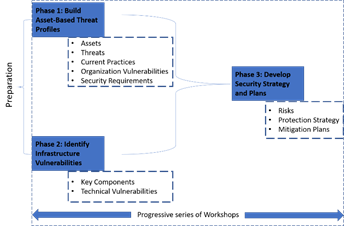
The below figure illustrates the typical steps involved in Threat Modeling,
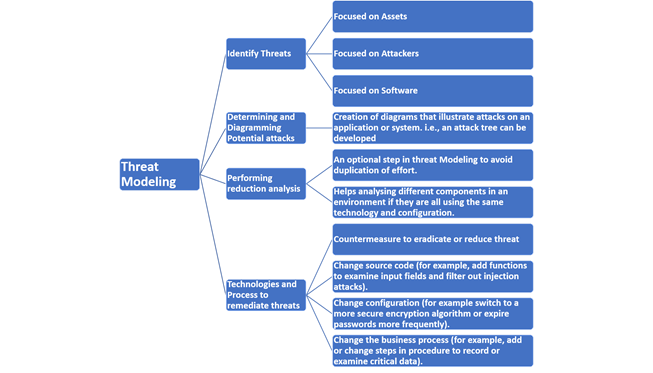
Analysts can use a combination of many threat models to create a robust and 360-degree view of potential threats. Not all of them are eclectic; some are abstract, and others are people-centric. Privacy concerns are the prime focus of some threat modeling methods. In this article, I summarize 12 available threat-modeling methods used to create a perception of potential attackers that includes their goals and focus on potential threats that may arise.
STRIDE
STRIDE is the most mature threat-modeling method and has evolved to include new threat-specific tables and the variants STRIDE-per-Element and STRIDE-per-Interaction. Data-flow diagrams (DFDs)are built using STRIDE to identify system entities, events, and the system’s boundaries. Microsoft primarily designed STRIDE to assess threats against application and OS.
STRIDE Threat Categories
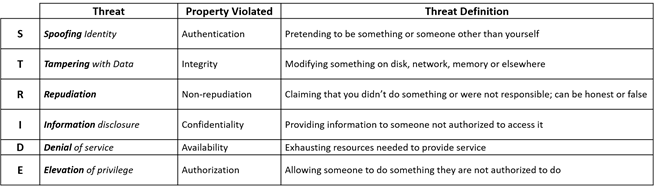
Microsoft also developed the DREAD (Damage Potential, Reproducibility, Exploitability, Affected users, Discoverability) method with a different approach for threats assessment.
PASTA
Process for Attack Simulation and Threat Analysis (PASTA) is a risk-focused approach where security countermeasures are applied to mitigate defined threat models, weaknesses, vulnerabilities, and attack vectors. It allows organizations to understand an attacker’s perspective on applications and infrastructure, thus developing threat management processes and policies.
Seven stages of PASTA

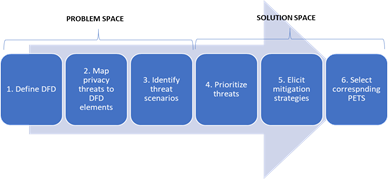
LINDDUN
LINDDUN (Linkability, Identifiability, Nonrepudiation, Detectability, Disclosure of information, Unawareness, Noncompliance) provides system analysts a systematic approach to privacy assessment and supports in eliciting and mitigating privacy threats in software architectures. Administrators can also use this method for data security.
LINDUN Steps
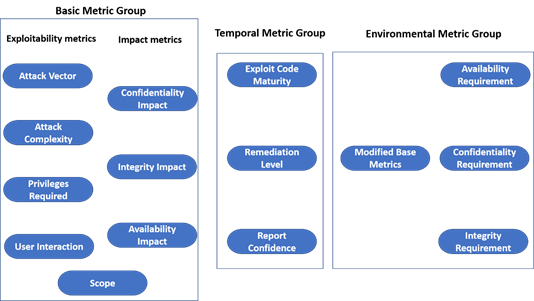
CVSS
The Common Vulnerability Scoring System (CVSS) summarizes the principal characteristics of a vulnerability and produces a numerical severity score. CVSS prompts the Organization and general users to prioritize their security responses and resources according to the threat.
CVSS v3.0 Metric Groups
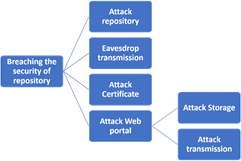
Attack Trees
Attack trees are conceptual diagrams that depict attacks on a system in tree form. The goal is the root node, and the different ways to achieve that are the leaf nodes. The nodes between the leaf node and the root node depict the intermediate states or attacker sub-goals.
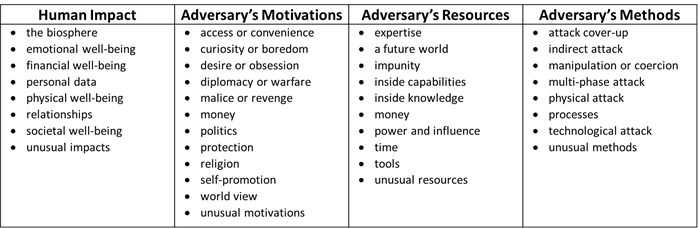
Security Cards
Security Cards identify unusual and complex attacks. They are not a formal method but, instead, a type of brainstorming technique. With the help of a deck of cards, analysts can answer questions about an attack, such as
- Who might attack?
- Why might the system be attacked?
- What assets are of interest?
- How can these attacks be implemented?
Security-Card Dimensions
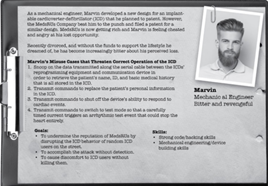
Persona non Grata
Persona non Grata (PnG) is a wargaming method for developing profiles for threat actors who could target the organization. The focus of this method is on the motivations and skills of the human attackers. The users are considered archetypes of those who can misuse the system and force analysts to view the system from an unintended-use perspective. It can help visualize threats from the counterpart side.
Example of Persona non Grata
hTMM
The Hybrid Threat Modeling Method (hTMM) is a combination of
- SQUARE (Security Quality Requirements Engineering Method) – a methodology designed to elicit, categorize, and prioritize security requirements
- Security Cards
- PnG – focus on the vulnerability of a system that an attacker can exploit. The method’s targeted characteristics produce zero false positives, no overlooked threats, consistent results, and cost-effectiveness.
The main steps of the method are:
- Identify the system to be threat modeled
- Apply Security Cards based on developer suggestions
- Remove unlikely PnGs which no realistic attack vectors could identify
- Using tool support, summarize the results from the above steps
- Continue with a formal risk-assessment method
Quantitative Threat Modeling Method
This hybrid method combines attack trees, STRIDE, and CVSS methods that work together. It addresses the pressing issues with threat modeling for cyber-physical systems that contain complex interdependences among their components.
Trike
Trike looks at threat modeling from a risk-management and defensive perspective. The analyst builds a risk-based approach with a unique implementation and risk modeling process. This model’s foundation is the ‘requirement model’ that ensures the risk assigned for each asset is ‘acceptable’ to the various stakeholders. An actor-asset-action matrix is created in which the columns represent assets, and the rows represent actors.
Each cell in the matrix is divided into four parts, one for each CRUD action (creating, reading, updating, and deleting). The analyst assigns one of three values in these cells: allowed action, disallowed action, or action with rules. Each cell is attached with a rule tree. With the requirement model in place, a data flow diagram (DFD) is created first. Each element is plotted to a selection of actors and assets. The analyst identifies threats by iterating through the DFD, which fall under one of two categories – elevations of privilege or denial of service. Each detected threat becomes a root node in an attack tree.
Trike uses a five-point scale for each action, based on its probability, to assess the risk of attacks that affect the assets through CRUD. The actors are evaluated on a three-dimensional scale (always, sometimes, never) for each action they may perform on each asset.
VAST Modeling
The Visual, Agile, and Simple Threat (VAST) Modeling method was conceived after reviewing the shortcomings and challenges of other methods. Its scalability and usability allowed it to be adopted across the infrastructure and the entire DevOps portfolio, integrated seamlessly into an Agile platform to provide actionable, accurate, and consistent outputs for developers, security teams, and senior executives alike.
VAST recognized the differences in operations and concerns among development and infrastructure teams and required creating two types of models:
- Application threat models – uses process-flow diagrams, representing the architectural point of view
- Operational threat models – created from an attacker’s point of view based on DFDs.
OCTAVE
The Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE) method define a risk-based strategic assessment and planning technique. It is heavy-weighted and focused on assessing organizational (non-technical) risks that may result from breached data assets. Its main aspects are an operational risk, security practices, and technology.
OCTAVE Phases
Threat modeling can help make the product more secure and reliable. This article presented twelve different methods that can be used alone or in conjunction with others. Choose the best method for a project based on the areas you want to focus on risk, security, privacy, the duration and experience you have with threat modeling, and most importantly, the stakeholder involvement. You can use these methods in an agile environment, depending on the timeframe and how often you need to repeat the modeling.
References
About the Author –

Vijayakumar V
Vijayakumar is a Technical Manager at GAVS and has over 10 years of experience in Cybersecurity across various Security sub-domains, including Network Security, Endpoint Security, Data Protection, Cloud Security, and Security Platform Management. He is an expert in analyzing Network logs, handling zero-day alerts, and hunting emerging threat campaigns. Vijayakumar has participated in the 2019 Capture The Flag (CTF) competition – Splunk Boss of the SOC (BOTS) in Malaysia and won his team’s second position among the ten South-East Asian competitors.
Back to blogs
