Complex IT landscapes, increasing sophistication of threats, cloud adoption, BYOD policies, and siloed IAM strategies are creating challenges in the management of identities & access, reducing security stature, mounting compliance concerns, and impacting user productivity & operational efficiency. This has mandated that comprehensive & cohesive identity & access management become part of strategic IT planning.
The Long 80 Approach
Tackling these challenges requires an in-depth understanding of the business and IT environments of the enterprise. The lack of a cohesive IAM strategy can lead to resource access mismanagement, poor end-user experience, and high administrative overhead. IAM implementations are long-term strategic projects that need to be aligned with business objectives.
Based on our experience, and learnings from customer engagements, we understand and tailor the fundamental business cases – IT Risk & Compliance, Operational & Cost Effectiveness, Business Enablement, Security – in accordance with business drivers. We extract the right set of elements from the business cases to craft a compelling roadmap and strategy for the deployment of a robust IAM solution.
We provide a manageable, scalable, efficient, and standards-based IAM solution that may be leveraged across businesses, platforms, and systems – and have been instrumental in the IAM transformation of global brands across industries. Our strong organization pedigree and robust partner ecosystem enable us to have a broad understanding of IAM products. Our IAM practice has defined a well-thought-out delivery cycle with a structured approach to effectively drive the IAM implementation while helping the business reap functional and operational benefits.
The Differentiators
- End-to-end IAM offerings with technical proficiency across multiple solutions
- A dedicated team of domain experts, architects, and designers
- Established knowledge repository with standards and proven frameworks for each industry
- Tailored approach to customization
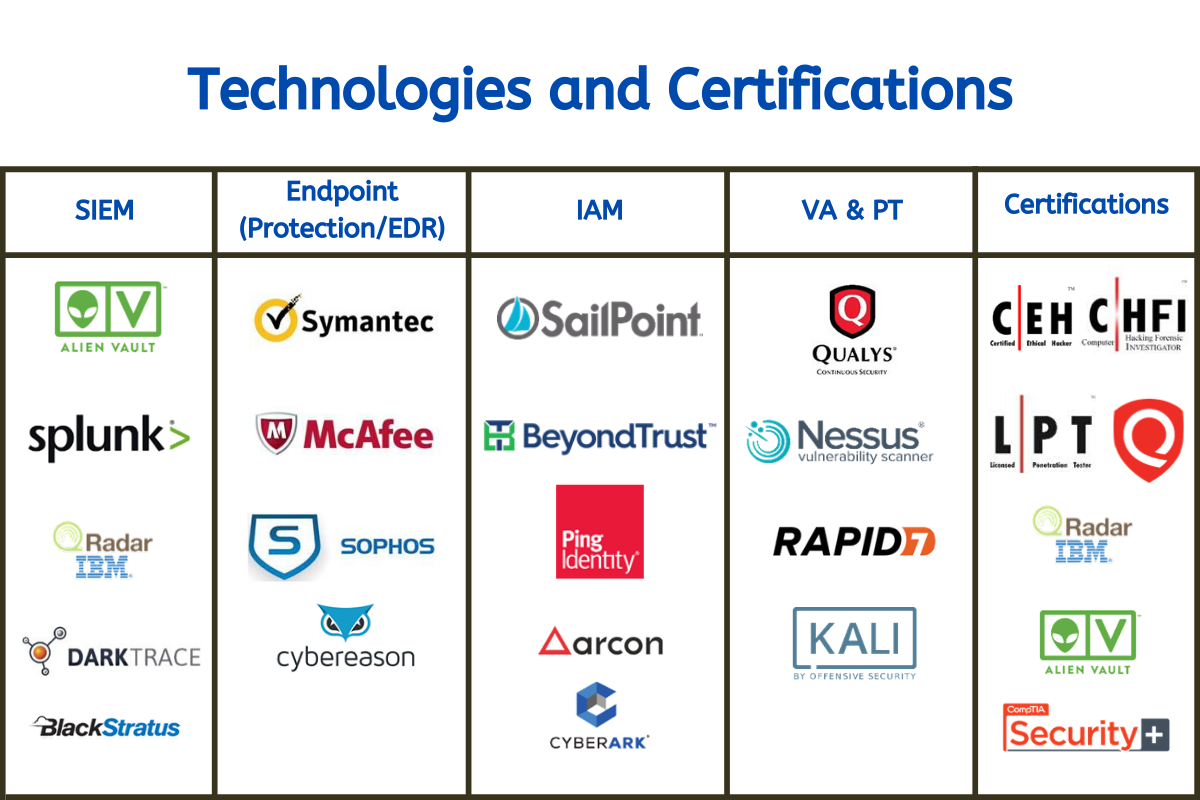
- Long-standing technology partnerships with industry-leading IAM vendors
- Year-on-Year TCO reduction
The Solutions
We have extensive experience and technical expertise in the complete identity management suite of solutions.
Identity Governance
- Identity Lifecyle Management
- Password Management
- Privileged Account Management
- Data Governance
Access Management
- Enterprise Single Sign-On (SSO)
- Web Single Sign-On
- Federation Services
- Role-based/Rule-based Authentication
Identity Providers
- Directory Services based on LDAP & Active Directory
- Cloud-based directory services and identity providers
The Engagement Model
We aim to build and implement a successful IAM solution that enterprises can leverage to enhance security, agility, and compliance while harvesting financial gains. As a strategy and planned implementation play a significant role in IAM projects, we employ our strong project management expertise coupled with technical know-how.
Advise – Getting Started
- Assessment
- Roadmap aligned to Business Objectives and Industry Trends
- Technology Evaluation & Selection
Partner Network
We have global partnerships with some of the leading technology vendors.