After going through a hectic week addressing Log4J vulnerability I was thinking what next and why do we need to go through sleepless nights to address a vulnerability. What if there is a solution that will prevent vulnerabilities from exploiting the application, “Tring…Tring…Hi, what is the status of the finance application. Have you tested the Server-Side Request Forgery fix.” Sounds familiar? Well you are not alone. Majority of the organizations today are in a similar situation.
What is Log4J?
Log4J a free open source software, it is a logging library for Java, which is widely used by majority of businesses applications and websites.
Apache Log4J is the most popular java logging library with over 400,000 downloads from its GitHub project. It is used by many companies worldwide, enabling logging in a wide set of popular applications. The Log4J library is embedded in almost every internet service or application including Twitter, Amazon, Microsoft, and so on.
What is Log4J vulnerability?
The Log4J vulnerability allows malicious attackers to execute code remotely on any targeted computer.
What is the impact?
A hacker can easily steal data or take control of your system over the internet. Check Point Software Technologies found that 24 hours after the initial outbreak, its sensors recorded almost 200,000 attempted attacks across the globe.
Log4J is considered to be the vulnerability of the decade. Likewise, there can be other vulnerabilities in the future that can give sleepless nights to application and security teams. If an organization is breached and the sensitive personal data of their customers are stolen, not only do they have to fix the issue, but also report it to authorities, pay penalties etc., resulting in reputational damage to the organization and hence impacting its business. This is definitely not a good situation to be in.
Firewalls and WAF are, in most cases, unable to detect and prevent such advanced attacks. This is where Runtime Application Self Protection from Hdiv comes in place. They are highly context aware and in a situation like this your application are protected from attacks.
RASP protects from Log4J automatically
RASP like one from Hdiv provides automatic protection from the CVE 2021-44228 with an ensemble of three protection features involved:
Untrusted Deserialization
For a vulnerability to be exploited an untrusted deserialization operation is required to load the malicious class from the external source and execute it in the application server. RASP has the ability to automatically block untrusted deserialization attacks
Micro-Segmentation
RASP, like one from Hdiv, can monitor and block remote call from the server to any untrusted remote servers. In the case of Log4J vulnerability, the exploit loads the executable code from a malicious server. This malicious server is controlled by the attacker.
Arbitrary Code Execution
RASP has the Arbitrary code execution monitoring feature. This feature will prevent the operating system to execute any malicious command and blocks the same. It can whitelist a function and prevent any command from execution within JVM.
What is Runtime Application Self Protection (RASP)?
Runtime Application Self Protection technology is a new layer of protection in addition to perimeter tools like firewall or WAF, that protects web applications from attacks during runtime. It’s a layer of protection that runs close to the application or on the application server. The tools used today are good and give a reasonable protection. Its goal is to prevent malicious actors from compromising internet applications and APIs by abusing coding vulnerabilities such as SQL Injection, Insecure Deserialization, XSS, etc.
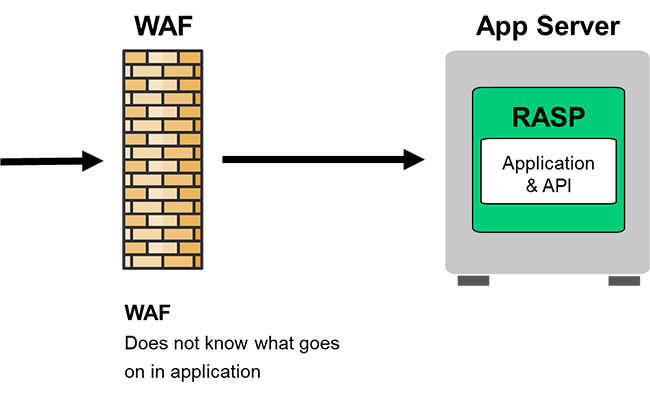
RASPs are an effective complement and/or upgrade from Web Application F products, a mainstream protection technology that is not adapting well to the new development approaches such as cloud deployments and DevOps methodologies. They are particularly recommended for systems where security is paramount because a RASP brings security in-depth and dramatically reduces the chances of security breaches.
The main advantages of this technology are accurately detecting vulnerabilities and intelligent decision making on what connections to block as we have all the context of the application.
How does RASP work?
RASP will have agents installed in the servers that acts as sensors for the application code which will monitor and control the execution. This protection happens in real-time during runtime. By means of those techniques, RASPs become part of the system so your applications remain protected wherever they go. As the acronym indicates, a RASP enables applications to protect themselves.
One of the main advantages of the RASP technology is its privileged point of view to conduct security analysis The point of view combines full visibility of the internal architecture details of the applications and full visibility of the execution flow during runtime. This means that a RASP can make smart decisions about what is an attack and what is not.
RASP is designed and architected in a way that it only looks into the vulnerable payload and protects them. This help to reduce the false positive alerts and saves lot of time for both security and application teams.
Many serious OWASP Top 10 risks, such as insecure deserialization and XML External Entity can only be protected effectively by a RASP, due to its combination of static and dynamic point of view.
What are the main benefits of RASP?
- Dramatic false positive reduction
- Strong protection, including zero-days
- Easy maintenance
- Easy DevSecOps support
What’s next?
Organizations that are using business critical applications should consider solutions like RASP from Hdiv. Doing a POC will give an idea what we have been missing all this while. Please reach out to us for any queries, we will be more than happy to guide you in the implementation journey.
About the Author –

Kannan Srinivasan
Kannan has over 21 years of experience in Cybersecurity and Delivery Management. He is a subject matter expert in the areas of Cloud security, infra security including SOC, Vulnerability Management, GRC, Identity and Access Management, Managed Security Services. He has led various security transformation engagements for large banks and financial clients.
Back to blogs
