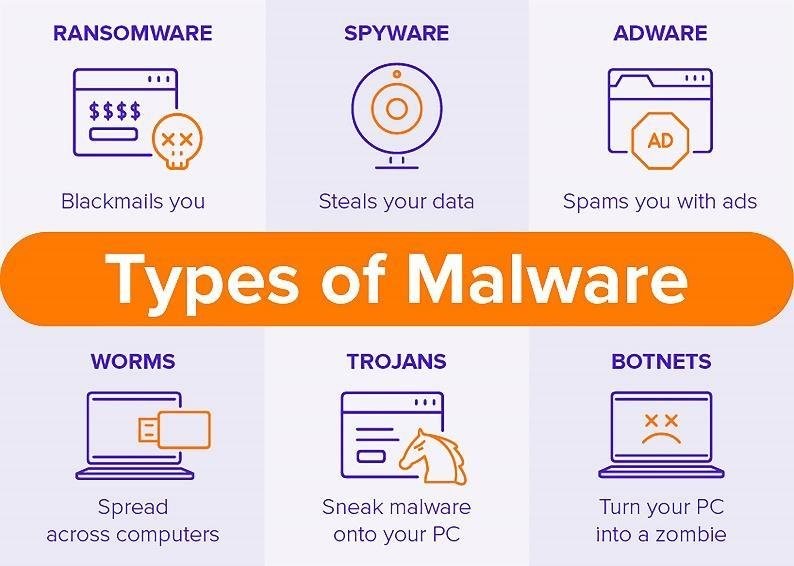
What is Malware?
Malware (MALicious softWARE) is an intrusive software that tries to execute unauthorized commands in the target system. The malware can exfiltrate data causing severe impacts on the target that falls victim. Malware attack vectors could be trojan horse or virus which are localized to infected system and worms which could infect the entire network.
Over the years, variety of malware attack vectors that can sneak their way into the IT exoskeleton of a company and malwares like rootkits, keyloggers, spyware, file infectors, ransomware etc. are used to compromise the targets effectively.
Incident Response
On an imminent security breach, incident response helps in reducing the loss of intellectual property and critical private data. Incident response programs strive to limit the damage of an attack, along with the cost of recovery. Incident response plan has several components like resource identification, preparation to technical investigation and containment, but malware analysis is one distinct area of security that has become increasingly beneficial to the process.
It helps responders understand the extent of a malware-based incident and identify additional hosts or systems that could be affected. Actionable information from malware analysis can help an organization more effectively mitigate vulnerabilities exploited by malware and help prevent additional compromise.
The Value of Malware Analysis for Successful Incident Response
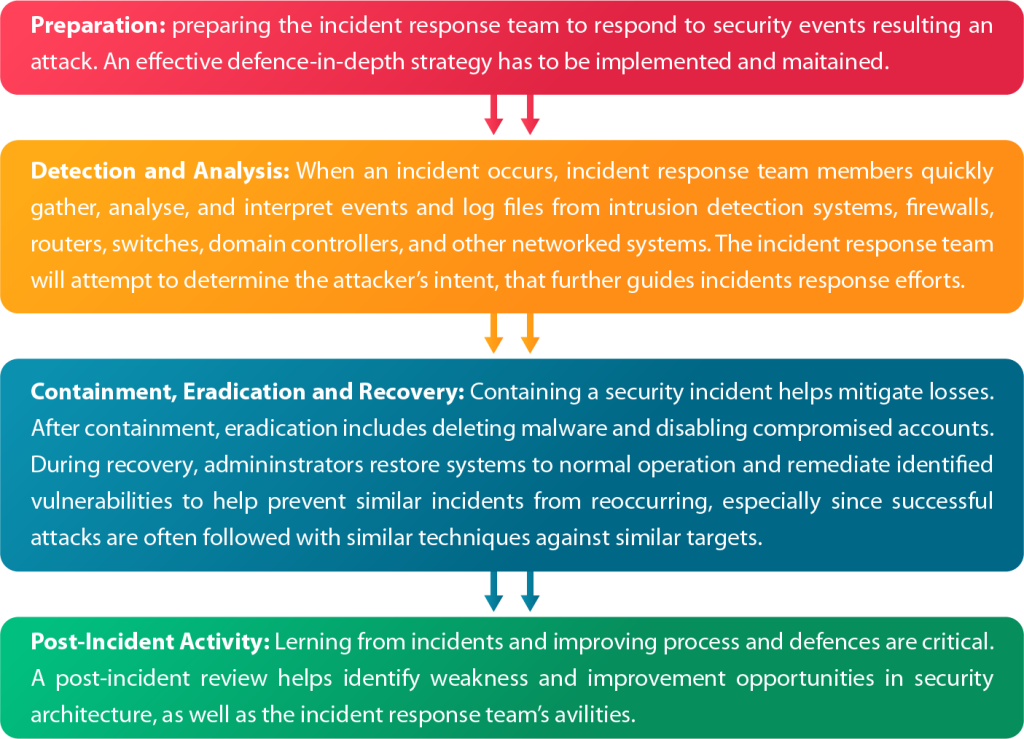
Malware analysis is applicable to all phases of incident response. The phases include preparation, detection and analysis, containment and eradication, and post-incident activity. Organizations should have their teams properly trained and equipped with responders who can quickly and effectively perform malware analysis. Without these resources, it’s hard to identify malware as the root cause of an incident. They may also take longer to contain incidents or fail to completely understand and eradicate malware from their networks, causing incremental damage and loss over time. The phases of incidence response are discussed in the picture below.
Phases of Incident Response
What if an Incident Occurs?
When malware is the source of a breach, knowledge of its capabilities and behaviour are crucial to effective incident response. Fast and reliable malware analysis can reveal the functionality of the malicious code. It can identify any changes the malware may have made to affected systems, and it can provide preliminary host and network-based indicators for detection signatures.
Malware analysis requires in-depth reverse engineering of malicious code and unknown software for a deep understanding of its capabilities, intent, attack vector, motivation, and tactics. Organizations should not be scrambling to find and equip malware analysts in the wake of a breach. With malware analysis, incident response program helps ensure a more swift and effective response and containment.
Advanced Malware Threats through Incident Response -> Value of Technical Indicators
The malware used in advanced threats are often undetected by common antivirus and network-based detection solutions. Targeted attacks using unique malware can successfully compromise the intended target.
Malware analysis reveals technical indicators that can be used to spot additional infections and compromised resources. These technical indicators contain forensic artifacts unique to the malicious code. They can relate to the way the malware behaves or the code itself and can be identified on a host or network.
Technical indicators include traditional forensic artifacts such as MD5 checksums, malware compile times, file size, name, path locations and registry keys. Technical indicators include domain names, IP addresses, email addresses, URIs or URLs, or any suspicious network communication. Advanced malware analysis techniques such as memory forensics analysis, identification of running process components, and imported/exported libraries used by an executable, are used to find the technical indicators.
Post-Incident Activity
Post-incident activity is probably the most important phase. During this phase, information learned by malware analysis should be documented and included in the incident summary reports or separate malware analysis documents for dissemination. The information should be used to help prevent future malware-based incidents of similar nature and bolster the capabilities to defend against future threats.
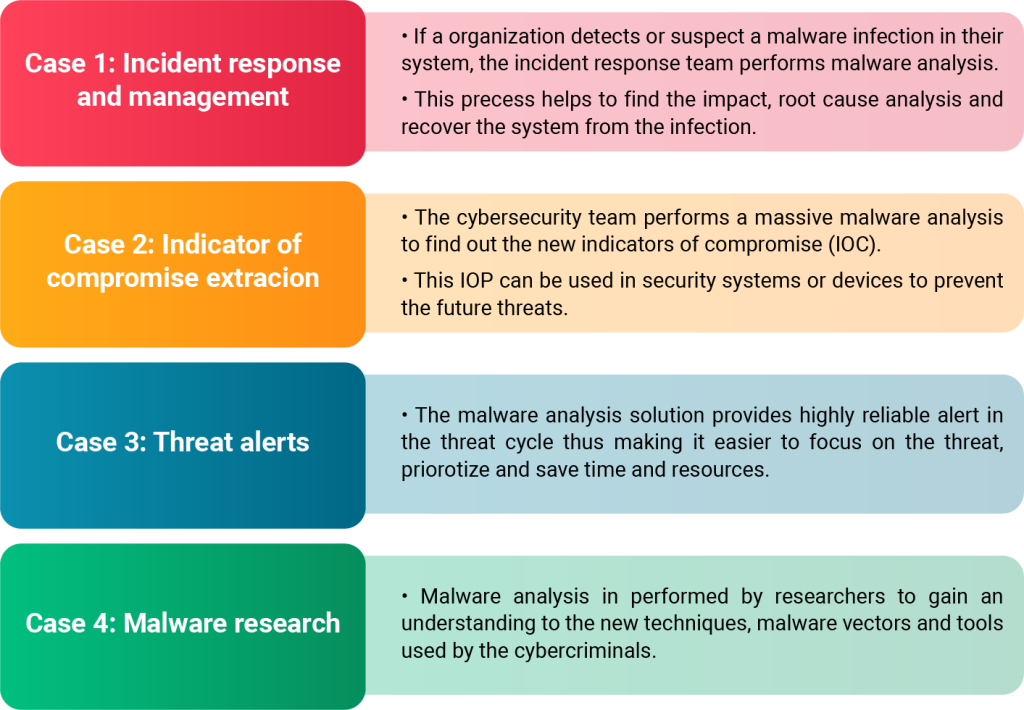
Malware Analysis
Malware analysis is the process of extracting information from a malware to study the origin, function, and impact of the malware. The main objectives of malware analysis are to:
- Identify and understand the type of malware and its functionality.
- Finding how the system is infected and define the severity of the attack.
- How cybercriminals communicate with the malware.
Malware analysis is an important constituent in the incident response plan and various use cases for malware analysis is shown in the diagram below.
Use cases for Malware Analysis
Types of Malware Analysis
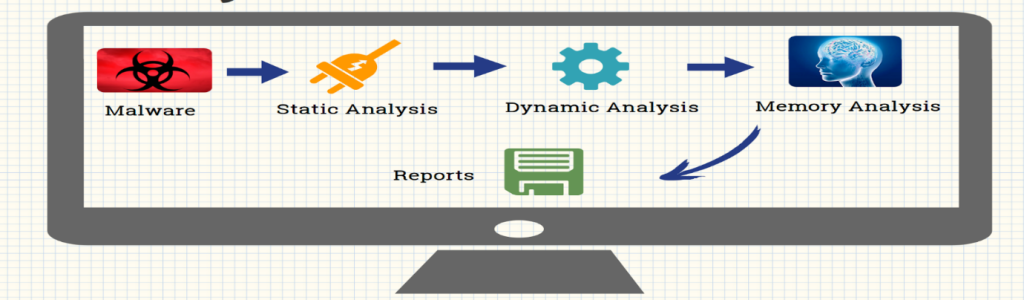
- Static Analysis: Static analysis is analyzing the software without executing it. It is simple but it cannot analyze sophisticated malware. Details like file type, encoded binary file, file obfuscations can be determined in static analysis.
- Dynamic Analysis: Dynamic analysis is executing the malware and observing its behavior while the infected system is isolated from the network. The responses to the malware requests are simulated to monitor the behavior. Dynamic analysis helps to remove the infection and focuses on consecutive activities, file system, registry, network, and system calls.
- Memory Forensics: Using a memory image to determine information about the programs, operating system, and state of the infected system. It involves memory acquisition and memory analysis. Memory forensics helps to congregate information like past and current network connections, keystrokes entered, open files and registry associated with the process, rootkit detection, code injection and other forensic artifacts.
Automating Malware Analysis
Automated solutions simplify malware analysis greatly by helping the analysts to check files, suspicious URLs, endpoints, and memory dumps at scale, instead of doing it manually. Automation saves time, effort and helps overcome the skills shortage. Automated solutions aren’t complicated, so beginner analysts can use them too.
Besides automation, practices that can be implemented for malware protection:
- Scanning systems regularly
- Employing security best practices like firewalls and anti-phishing prevention
- Creating regular backups
- Updating systems and applications regularly
- Employing measures to prevent social engineering attacks
Importance of Malware Analysis in an Organization
With malware causing so many security breaches, strong analysis is required for effective incident response. So, organization should conduct 24/7 security threat research, vulnerability analysis and incident response. An incident response program that includes expert malware analysis helps responders identify malware-based incidents and understand their ramifications. Actionable information and early intelligence from malware analysis can help an organization be more aware and help prevent additional compromise.
References:
Sources:
- https://www.researchgate.net/profile/Mariwan-Ahmad/publication/340770783/figure/fig1/AS:882090539233283@1587318181208/Types-of-Malware-7.jpg
- https://www.yeahhub.com/wp-content/uploads/2017/01/malware.png
About the Author –

Vishnu Raj
Vishnu Raj is a part of the GAVS Security Practice (Red Team Member). He’s passionate in building secure apps as he believes everyone deserves privacy.
Back to blogs
