On May 12, 2021, US President Joe Biden signed an Executive Order to Improve the Nation’s Cybersecurity and Protect Federal Government Networks. On July 28, 2021, President Biden signed a National Security Memorandum (NSM) on Improving Cybersecurity for Critical Infrastructure Control Systems. The Executive Order for cybersecurity defense strategies was signed in the wake of several notable cybersecurity attacks in 2020 and 2021 faced by public and private sector entities targeted by both nation-state actors and cybercriminals. The Solar Winds hack that compromised many federal agencies, the ransomware attack targeting the Colonial Pipeline, the Microsoft Exchange Server vulnerabilities that affected several thousand organizations across the globe are a few such examples. These incidents share commonalities, including insufficient cybersecurity defense mechanisms that leave public and private sector entities more vulnerable to data breaches.
The Executive Order also galvanizes public and private sector efforts to assist identify, deter, protect against, detect, and respond to persistent and increasingly sophisticated malicious cyber threat campaigns. The federal government must also carefully investigate what occurred during any major cyber incident, employ lessons learned, and partner with private sector for protecting nation the from cyber threat actors. The private sector must adapt to the continuously changing threat environment, ensure to build products to operate securely, and partner with the Federal Government to foster a safer cyberspace. The Executive Order emphasizes the importance of protecting the “computer systems, whether or not they are on-premises, cloud-based, or hybrid” and extends the scope to incorporate systems that process data and run crucial machinery paramount to the nation’s safety.
What does the Executive Order mean for organizations?
The Executive Order outlines the following decisive steps to modernize its approach to Cybersecurity.
Modernize Federal Government Cybersecurity
- Adopt Cybersecurity Industry Best Practices
- Secure cloud services (private, public, hybrid and multiclouds)
- Advance towards Zero Trust architecture and implementation
- Employ Multi-factor Authentication(MFA)
- Encrypt data-at-rest and data-in-transit
Enhance Software Supply Chain Security
- Protect integrity of critical software
- Employ encryption of data everywhere
This requires massive review of all cybersecurity practices and establish consistent guidelines which agencies will need to implement in the short, mid, and longer term based on the residual risk of each identified items. However, agencies are already obliged to take immediate actions aimed at modernizing Federal IT architecture and improving Cybersecurity posture. These include:
- Within 60 days, agencies will be required to:
- Update plans to prioritize the adoption and use of cloud computing technology
- Develop a strategy for Zero Trust security architecture design and implementation
- Within 180 days, agencies will be required to adopt encryption for data-at-rest and data-in-transit and multi-factor authentication (MFA) for users.
The White House also published a factsheet which highlights the SEVEN key points that the Executive Order looked to address:
- Remove Barriers to Threat Information Sharing Between Government and the Private Sector
- Modernize and Implement Stronger Cybersecurity Standards in the Federal Government
- Improve Software Supply Chain Security
- Establish a Cybersecurity Safety Review Board
- Create a Standard Playbook for Responding to Cyber Incidents
- Improve Detection of Cybersecurity Incidents on Federal Government Networks
- Improve Investigative and Remediation Capabilities
The White House also highlights Department of Homeland Security’s (DHS) recent Security Directive to enable critical pipeline owners and operators to implement several urgently needed protections, including:
- Implementing mitigation measures to protect Operational Technology (OT)assets and Information Technology (IT)systems against ransomware attacks and other known and unknown threats.
- Developing and implementing a cybersecurity contingency plan and recovery plan.
- Conducting periodic or at least annual cybersecurity non-disruptive studies of architecture design review.
The pinnacle of this directive needs not just the federal government, but public and private sector entities to help to secure our critical infrastructure.
About GAVS Cybersecurity Services
Prepare – Protect – Proactively Respond
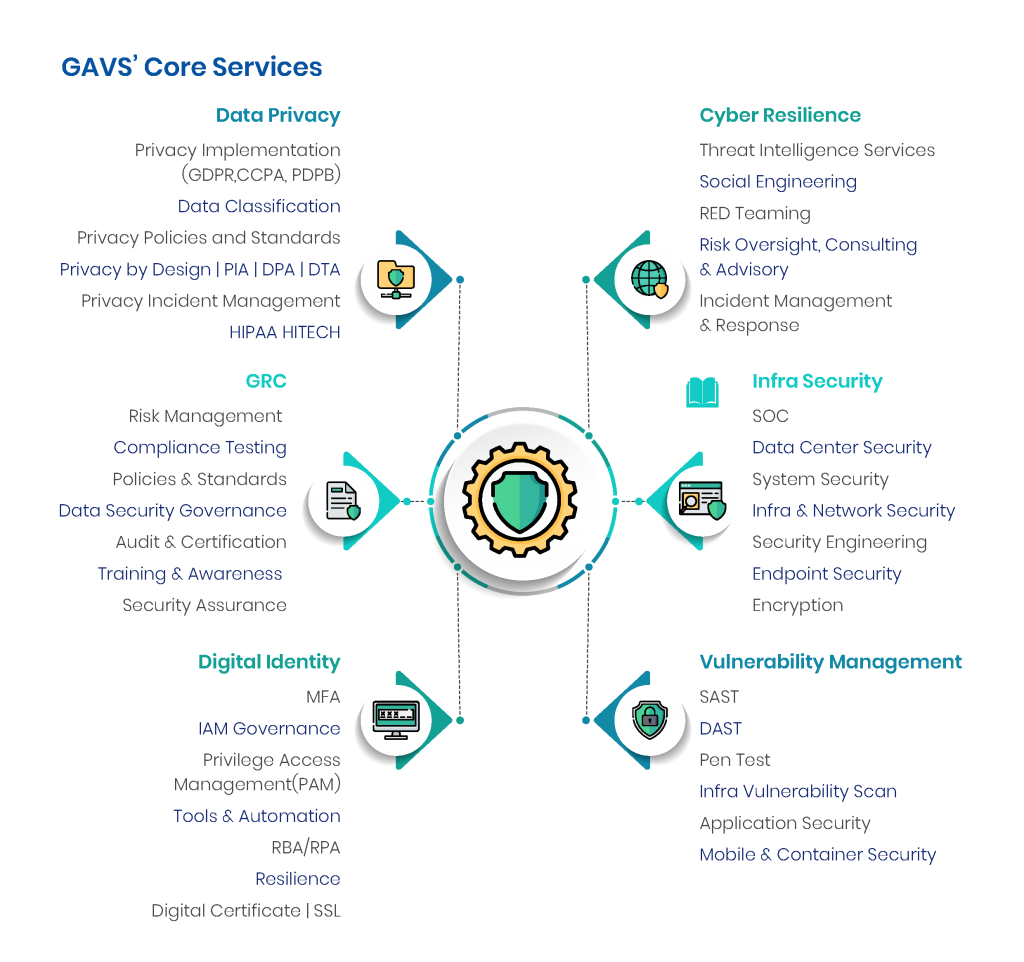
GAVS delivers end-to-end Cyber Security Services, helping clients manage risk and build an effective cyber security program. GAVS caters to the full suite of organizational cyber security needs – assessment, operations, and/or strategy – and can help conquer your most critical cyber security issues. GAVS is consistently recognized in reports from analyst firms like Everest, in IT Security & Healthcare IT Security PEAK MatrixTM.
What’s Next? If you would like to learn more about Best Practices for Implementing the White House Executive Order and how GAVS allies and delivers end-to-end Cybersecurity services to its customers, please visit www.gavstech.com or get in touch with us at inquiry@gavstech.com
About the Author –

Alex Lawrence
Alex brings with him 15 years of experience in Cybersecurity and currently focused on solving cyber puzzles for Healthcare Industry. He also plays vCISO role for a key GAVS Healthcare client based out of New York City. He is an experienced Technologist and Leader mentors Cybersecurity Operations, Security Incident Detection and Response, Security Automation, Cyber Threat Intelligence, Cloud Security, Vulnerability Management, Supply Chain Cyber Risk, Medical Device and Clinical Application Security. Back to blogs

